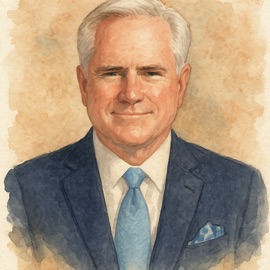
Craig Housley (Robert Craig Housley) – referenced in the Fiber Network Solutions (FNSI) investigative record
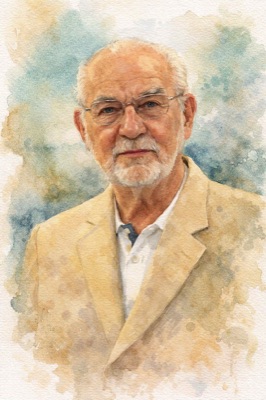
Inga Housley (Ingeborg L. Housley) – referenced in the Fiber Network Solutions (FNSI) investigative record
Disclaimer and Legal Context
This page identifies individuals who, based on documented evidence and good-faith analysis, are reasonably believed to have participated in, enabled, or failed to act in connection with the fraudulent acquisition of Fiber Network Solutions, Inc. and its subsequent concealment. The information presented here has been submitted in formal whistleblower disclosures to the U.S. Securities and Exchange Commission, the Department of Justice, the Internal Revenue Service – Criminal Investigation Division, and other federal agencies.
This list does not assert criminal guilt. Instead, it reflects a factual and evidentiary account of each individual’s known or alleged role, behavior, or response pattern—particularly where actions or omissions may be relevant to public interest, fiduciary duty, or federal investigations.
This page is published in accordance with protections under federal whistleblower law and the First Amendment of the United States Constitution.
This is not a cold case. The applicable statute of limitations remains open under established federal tolling doctrines.
The Broader Network of Responsibility for the Fraudulent Transfer of Fiber Network Solutions, Inc. (FNSI to Cogent Communications, Inc. (NASDAQ: CCOI)
The 2003 acquisition of Fiber Network Solutions, Inc. (FNSI) by Cogent Communications was not an isolated act of misconduct. Evidence submitted in federal whistleblower filings shows a coordinated pattern involving multiple participants—executives, accountants, attorneys, IT administrators, and consultants—who contributed to or benefited from the concealment of material facts.
Digital forensics, internal communications, and archived documents demonstrate deliberate suppression of evidence, the misuse of confidential data, and false reporting that sustained the cover-up for more than two decades.
Under the Racketeer Influenced and Corrupt Organizations Act (RICO), 18 U.S.C. § 1962, any individual who knowingly participates in, facilitates, or profits from an enterprise engaged in fraud may face criminal liability. All applicable statutes of limitations have been reset in accordance with statutory law and controlling case precedent.
This section exposes the broader ecosystem of complicity surrounding the FNSI–Cogent Communications transaction and the continuing pattern of concealment revealed through authenticated corporate records, network analytics, and whistleblower submissions to the DOJ, SEC, and IRS-CI.
For an in-depth, comprehensive overview of the documentary timeline regarding the fraudulent acquisition of Fiber Network Solutions, Inc. by Cogent Communications (NASDAQ: CCOI), visit the Download PDF's page, or read the html versions at the Read Doc's On-Line page.
A 160-page evidentiary report, supported by primary source documents, recordings, and contemporaneous records, identifies multiple independent bases under federal law for tolling and extending the statute of limitations for both civil and criminal claims arising from the 2003 transaction and its subsequent concealment.
These bases fall into two distinct but reinforcing legal frameworks: (1) the discovery rule, and (2) continuing and ongoing concealment.
⸻
The Discovery Rule — Independent Tolling Basis
Under the federal discovery rule, a statute of limitations does not begin to run until the injured party discovers — or, through reasonable diligence, should have discovered — the existence of the fraud and the resulting injury.
David J. Koch’s first documented indication that he had been defrauded occurred on or about January 30, 2025, when an email exchange with Kyle Bacon, combined with a review of archived corporate records, revealed the deliberate nature of the underlying transaction.
Prior to that date, the structure and consequences of the transaction — including the use of a proxy, the omission of material schedules, undisclosed distributions, and coordinated concealment — were not reasonably discoverable due to sustained and active concealment.
Under the discovery rule, any applicable limitations period did not begin to run before that date.
⸻
Continuing Concealment — Ongoing Tolling
The tolling analysis does not end with discovery. It extends to the present.
The schedules to Exhibit 2.5 of Cogent’s 2004 S-1 registration statement — documents that would disclose the full financial structure of the transaction — have never been produced.
Despite formal written demands and notice, Cogent Communications has refused to provide these materials.
On May 23, 2025, Cogent’s Chief Legal Officer, John Chang, confirmed in writing:
“You are not entitled to those materials and we are not obligated to provide those to you.”
This refusal constitutes a documented, ongoing act of concealment occurring in 2025.
Under the doctrine of fraudulent concealment, the statute of limitations is tolled for as long as the defendant continues to actively withhold material information necessary to fully discover the claim.
Because the Exhibit 2.5 schedules remain withheld, the concealment that began in 2003 has not been resolved.
⸻
Resulting Limitations Framework
Two independent conclusions follow:
First, under the discovery rule, no limitations period began prior to January 30, 2025.
Second, under continuing concealment, there is a legally supportable basis that the limitations period remains tolled to the present due to ongoing withholding of material information.
Each doctrine independently defeats a statute of limitations defense. Together, they establish a continuous and uninterrupted limitations framework extending into the present.
⸻
Key Case Law:
Holmberg v. Armbrecht, 327 U.S. 392 (1946)
Klehr v. A.O. Smith Corp., 521 U.S. 179 (1997)
Merck & Co. v. Reynolds, 559 U.S. 633 (2010)
United States v. Smith, 740 F.2d 734 (9th Cir. 1984)
United States v. Arnold, 117 F.3d 1308 (11th Cir. 1997)
United States v. Levine, 457 F.2d 1186 (10th Cir. 1972)
Toussie v. United States, 397 U.S. 112 (1970)
⸻
Statutory Violations Referenced
18 U.S.C. § 371 — Conspiracy to defraud the United States
18 U.S.C. § 1001 — False statements and concealment of material facts
18 U.S.C. § 1510 — Obstruction of criminal investigations
18 U.S.C. § 1512 — Witness tampering and interference with evidence
18 U.S.C. § 4 — Misprision of felony
18 U.S.C. § 3282 — General federal statute of limitations (non-capital offenses)
18 U.S.C. § 1030(a)(2) — Unauthorized access to protected computers
18 U.S.C. § 1030(a)(5) — Intentional damage to protected computers
18 U.S.C. § 1030(b) — Conspiracy and attempt under the Computer Fraud and Abuse Act
18 U.S.C. § 1029 — Fraud involving access devices
For more than twenty years, the individuals who engineered the 2003 FNSI–Cogent transaction operated under the assumption that the passage of time had insulated their conduct from scrutiny. The evidentiary record now indicates that assumption is no longer valid.